
SCOM 2016 web console hot fix
Security teams may be contacting you for CVE-2020-1331 vulnerability on the 2016 web console. In my example, the Tenable scanner listed ALL SCOM management group servers – under SCOM2016/2019).
NOTE KB does not install on server, so does not show up under ‘Installed Updates’
Background
HotFix DLL comes with a readme to replace the DLL for the SCOM 2016 WebConsole role
If you don’t already know this, the roles each get their own directory on your SCOM server
Security scanners run scripts to help validate if system is vulnerable. It is possible that the scanner is just looking for some string for the install of SCOM, NOT the actual role that is vulnerable.
SCOM 2016 typically installs @ (‘\Program Files\Microsoft System Center 2016’)
SCOM 2019 typically installs @ (‘\Program Files\Microsoft System Center’)
Identify SCOM roles
Open PowerShell window to identify roles
cd “D:\Program Files\Microsoft System Center 2016\Operations Manager”
Resolve Web Console vulnerability
High level steps
Download the KB here
Execute KB
Copy dll and readme file
Backup DLL and replace
Reboot server
Contact Security Team to re-scan server
Mitigate vulnerability
Download the KB here
Extract downloaded the KB
Click Run to extract, and list extraction path

Copy Windows Explorer Path you want to extract to, and paste in the path
Example
S:\MonAdmin\MSDN images\SCOM\2016\WebConsole HotFix

Copy current DLL & replace with hotfix DLL
Open PowerShell window (as admin)
# Backup DLL
# Change Drive letter if you hopefully installed SCOM on D: drive (non-system drive)
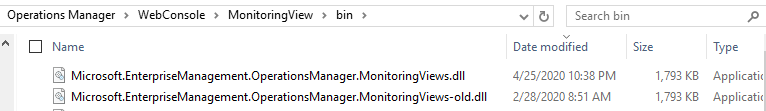
copy “C:\Program Files\Microsoft System Center 2016\Operations Manager\WebConsole\MonitoringView\bin\Microsoft.EnterpriseManagement.OperationsManager.MonitoringViews.dll” “C:\Program Files\Microsoft System Center 2016\Operations Manager\WebConsole\MonitoringView\bin\Microsoft.EnterpriseManagement.OperationsManager.MonitoringViews-old.dll”
# Replace DLL
copy “C:\MonAdmin\Microsoft*.dll” “C:\Program Files\Microsoft System Center 2016\Operations Mana
ger\WebConsole\MonitoringView\bin”
# Verify
cd “D:\Program Files\Microsoft System Center 2016\Operations Manager\WebConsole\MonitoringView \bin”
gci Microsoft.EnterpriseManagement.Operations*.dll
Sample screenshot from Windows Explorer view of Bin directory for replaced DLL – Same size, only timestamp changes July Page 4
Reboot server
Test WebConsole functionality
Verify from SCOM Console > Administration Tab > Settings > Web

Example
http://16ms01/OperationsManager
Contact Security Team to re-scan SCOM asset(s)
References
CVE-2020-1331 https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2020-1331
Microsoft Support article
Tenable forum post https://community.tenable.com/s/question/0D53a000074LGapCAG/plugin-137369-security-updatesfor-microsoft-system-center-operations-manager
