Sometimes as the monitoring admin, you may be responsible to secure your servers, being told from Security/Cyber Teams about new vulnerabilities. The vulnerabilities may be from Tanium, ACAS, Tenable or other security tools. This article is how to help you secure related SCOM web console, and SSRS reporting sites against Unconstrained Delegation vulnerabilities CVE-2020-17049, also AD STIG V-36435.
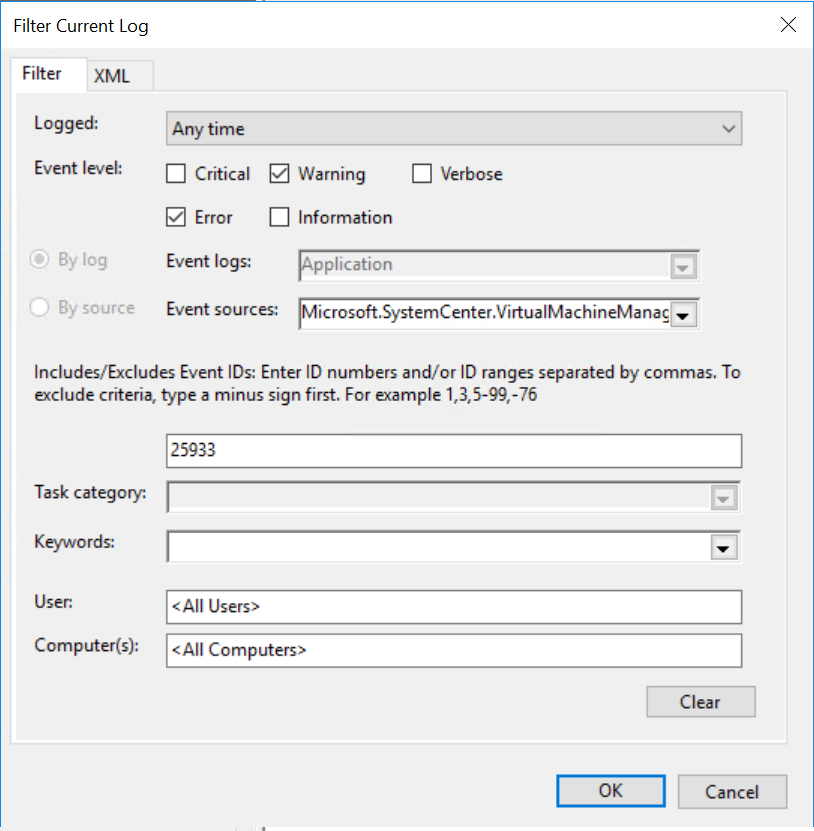
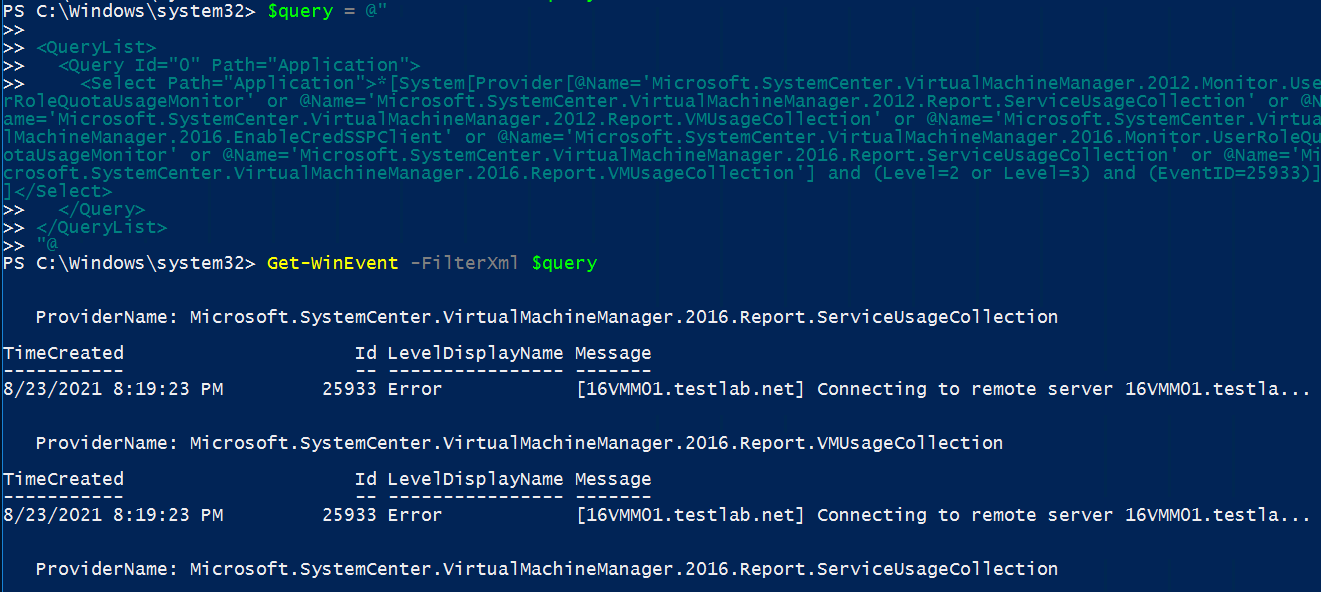
First we need to identify IF this is a true finding.
Typically this comes from Server/SystemsAdmin with domain admin access:
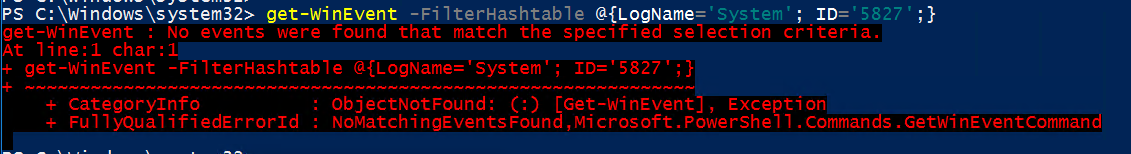
From PowerShell run:
Get-ADComputer -LDAPFilter
“(userAccountControl:1.2.840.113556.1.4.803:=524288)”
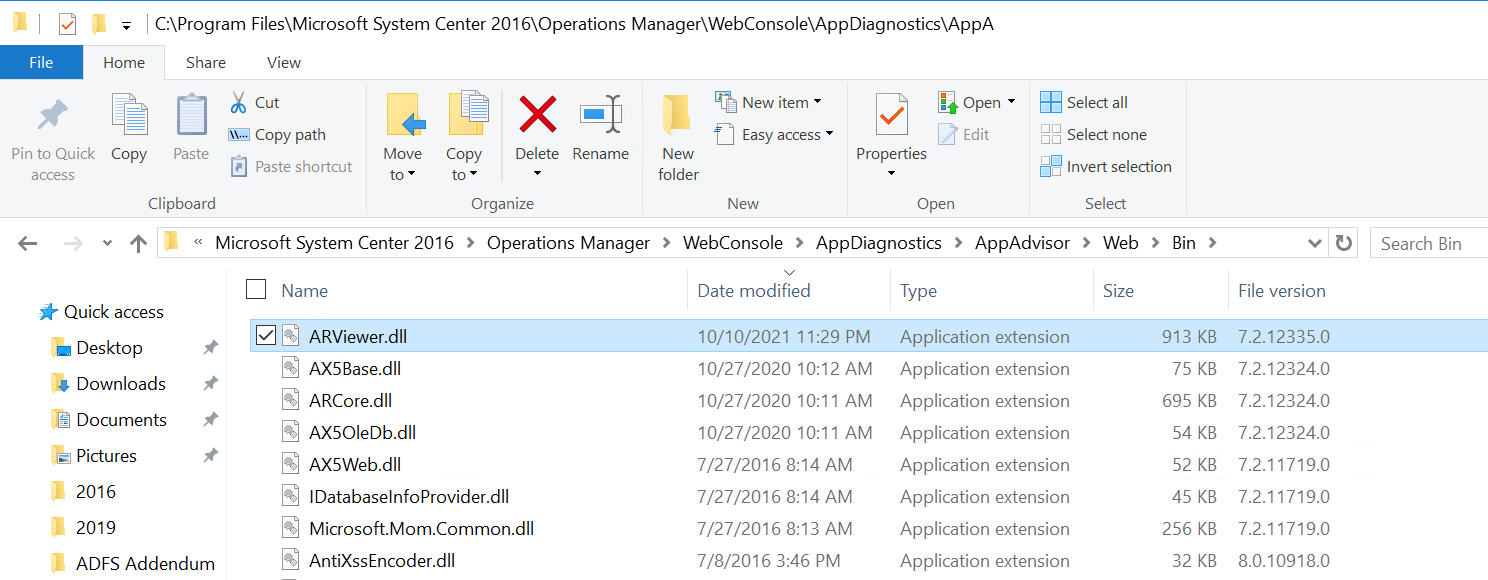
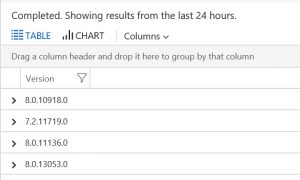
After identifying SCOM servers with unconstrained delegation (scope of blog post is focused on SCOM in a hybrid scenario (prem/cloud), we need to resolve.
With domain administrator rights, open the Active Directory Users and Computers MMC snap-in.
In ADUC, change Find drop-down to Computers
In the Computer name text box, enter <SCOMServer> and click search
Right click the server in the results box > Select Properties.
Select the Delegation tab.

Select Trust this computer for delegation to specified services only > Use any authentication protocol.
Under Services to which this account can present delegated credentials, select Add.
In the new dialog box, select Users or Computers.
Enter <SCOMServer>, and then select OK.
Click the Add button to add services
Select the w3svc and www processes
Select OK.

Once set in AD, reboot server. Running ‘gpupdate /force’ may not apply AD changes to the server object.
After reboot, reach out to SCOM Admins to test webconsole authentication
From edge browser, go to SCOM web console, typically @ https://<SCOMServer>/OperationsManager
On the Monitoring tab, click on Active Directory dashboard on left
Verify authentication works
Documentation
Pentestlab – Detecting Unconstrained Delegation Exposures in AD Environment
Petri.com find and block unconstrained delegation
Learn.Microsoft.com unconstrained kerberos article
Explanatory documents on what/why