Have you ever needed to find the command UNIX pack runs for perf counter? Say the processor time value doesn’t match what the Unix admin may be saying SCOM is showing.
Many times you can look at the SCOM management pack, and those commands trace back to the UNIX library.
Background: The SCOM management server runs many of the cross-plat/xplat workflows to the UNIX agent through WinRM.
Agenda
- Unseal SCOM UNIX management pack to obtain URI
- Understand command line options from UNIX/Linux side, and how to view the output
- Enumerate command line
- Test Command line from SCOM MS
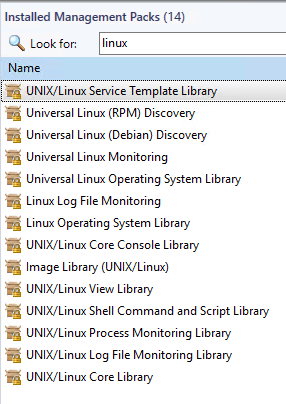
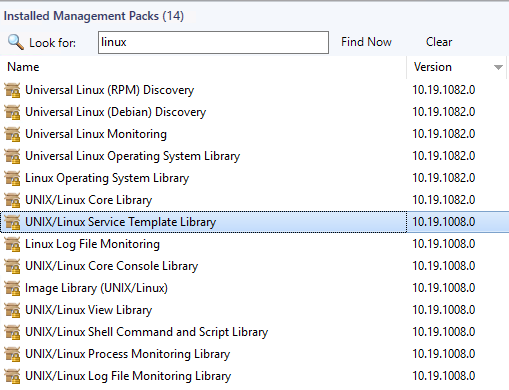
Unseal SCOM UNIX management pack
The screenshot below is unsealing the Solaris10 pack to XML, and then viewing/searching to show the processor reference.
Solaris 10 processor rules
NOTE that’s a URI, not a script
How UNIX admin may supply processor output
Example – Unix admin typically uses vmstat or iostat.
The screenshot uses ‘vmstat 2 10‘ – a snapshot every 2 second intervals, 10 times

We can discuss the vmstat output, but it shows way more than just processor (ready queue, swap, user, system, and cpu %) to help figure out which operating system component is the problem.
Enumerate command line test
How do we test the command line syntax, to verify what SCOM pulls when running the rule?
For example, we need to make the URI actionable from the management pack. What is needed to make a usable command?
Grab the URI from the pack –
http://schemas.microsoft.com/wbem/wscim/1/cim-schema/2/SCX_ProcessorStatisticalInformation?__cimnamespace=root/scx
Because we know the URI, we now build out the syntax with WinRM
winrm enumerate http://schemas.microsoft.com/wbem/wscim/1/cim-schema/2/SCX_ProcessorStatisticalInformation?__cimnamespace=root/scx -auth:basic -remote:https://<servername>:1270 -username:<scomID, not necessarily root> -skipCACheck -skipCNCheck -skiprevocationcheck –encoding:utf-8
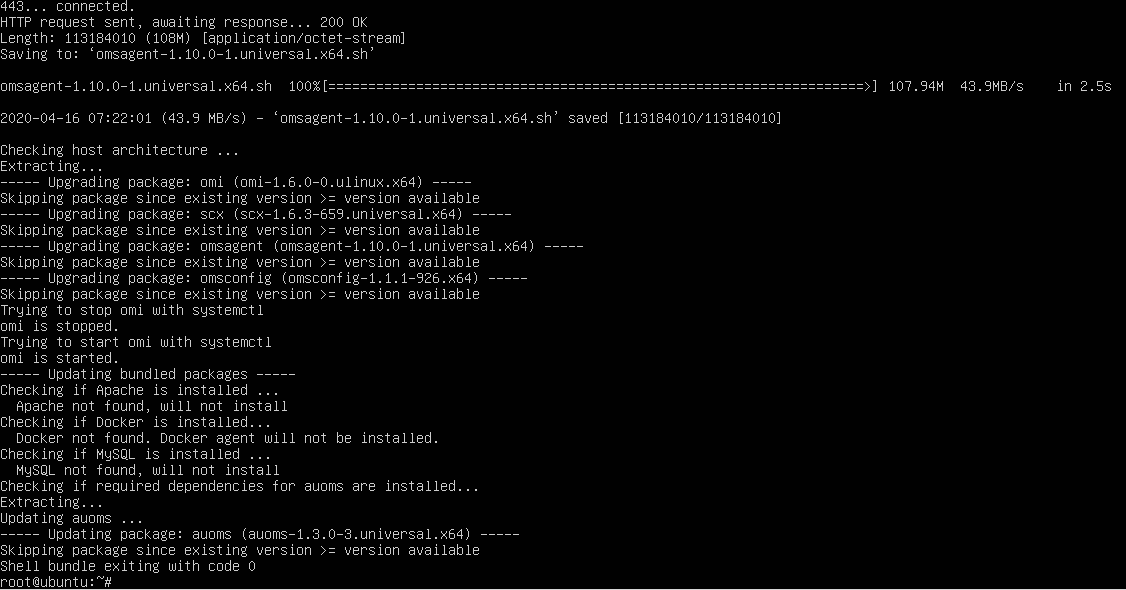
Test WinRM command from SCOM MS
For instance, we want to test the WinRM command from the MS to the UNIX server
winrm enumerate http://schemas.microsoft.com/wbem/wscim/1/cim-schema/2/SCX_ProcessorStatisticalInformation?__cimnamespace=root/scx -auth:basic -remote:https://ubuntu:1270 -username:scom -skipCACheck -skipCNCheck -skiprevocationcheck –encoding:utf-8
Example output
SCX_ProcessorStatisticalInformation
InstanceID = null
Caption = Processor information
Description = CPU usage statistics
ElementName = null
Name = 0
IsAggregate = FALSE
PercentIdleTime = 99
PercentUserTime = 0
PercentNiceTime = 0
PercentPrivilegedTime = 0
PercentInterruptTime = 0
PercentDPCTime = 0
PercentProcessorTime = 1
PercentIOWaitTime = 0
SCX_ProcessorStatisticalInformation
InstanceID = null
Caption = Processor information
Description = CPU usage statistics
ElementName = null
Name = _Total
IsAggregate = TRUE
PercentIdleTime = 99
PercentUserTime = 0
PercentNiceTime = 0
PercentPrivilegedTime = 0
PercentInterruptTime = 0
PercentDPCTime = 0
PercentProcessorTime = 1
PercentIOWaitTime = 0
Additional references for WinRM syntax and troubleshooting
Use Unix MP’s for shell commands