First, use SCOM helper for advanced administration (a shameless plug to Tyson & MonitoringGuys blog!)

In case you didn’t know, as I may be the last off the airplane, it’s time to talk about SCOMHelper. Things you forget, like using a power drill, versus manual screwdriver, all because you’re familiar with the old trusty screwdriver. Man, I think I upgraded past the power drill with a cord, to a lithium-ion powered impact drill with SCOMHelper.
Blog https://monitoringguys.com/2019/11/12/scomhelper/
Download https://www.powershellgallery.com/packages/SCOMHelper
Install SCOMHelper
Time to use SCOM helper for advanced administration, and get it installed!
Pretty simple install. I would recommend adding to monitoring team server, jumpserver, from SCOM MS, or console enabled, Operations Manager plug-in installed machines.
From PowerShell (as admin)
Install-Module -Name SCOMHelper
SCOM helper functions
Clear-SCOMCache Compare-String Deploy-SCOMAgent Export-SCOMEffectiveMonitoringConfigurationReport Export-SCOMEventsToCSV Export-SCOMKnowledge Export-SCOMOverrides Fast-Ping Get-SCOMAlertKnowledge Get-SCOMClassInfo Get-SCOMHealthCheckOpsConfig Get-SCOMMPFileInfo Get-SCOMRunAsAccountName Get-SCOMRunAsProfilesAccounts Get-SCOMRunningWorkflows Get-StringHash New-SCOMClassGraph New-SCOMComputerGroup Ping-AllHosts Remove-SCOMObsoleteReferenceFromMPFile Set-SCOMMPAliases Show-SCOMModules Show-SCOMPropertyBag Test-Port Unseal-SCOMMP Update-SCOMComputerGroup Start-SCOMOverrideTool
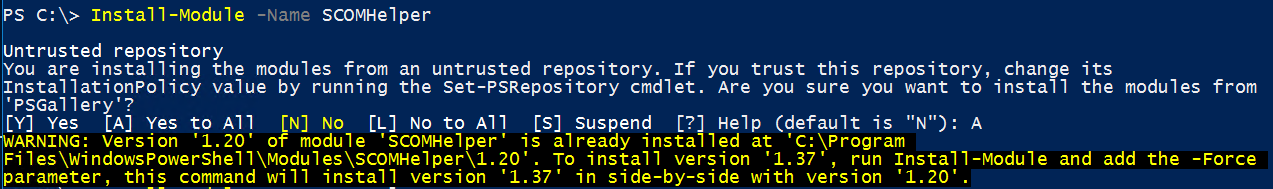
Open PowerShell (as admininstrator)
Type: Install-Module -Name SCOMHelper
Example output
PS C:\> Install-Module -Name SCOMHelper
Untrusted repository
You are installing the modules from an untrusted repository. If you trust this repository, change its
InstallationPolicy value by running the Set-PSRepository cmdlet. Are you sure you want to install the modules from
‘PSGallery’?
[Y] Yes [A] Yes to All [N] No [L] No to All [S] Suspend [?] Help (default is “N”): A
If SCOMHelper is already installed
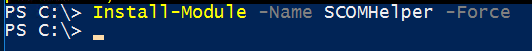
Open PowerShell (as admininstrator)
Type: Install-Module -Name SCOMHelper -Force
(You may get the untrusted repository message if you answered Y (yes) or N (no)
Example output
PS C:\> Install-Module -Name SCOMHelper -Force
PS C:\>
Just one example –
Use the Unseal-SCOMMP to unseal your MP and MPB’s for your SCOM mgmt pack repository
Have fun playing!
If you’re administering management groups, I can pretty much guarantee you will need these:
Export-SCOMEffectiveMonitoringConfigurationReport
Export-SCOMOverrides
Get-SCOMHealthCheckOpsConfig
Get-SCOMRunningWorkflows
New-SCOMClassGraph
Remove-SCOMObsoleteReferenceFromMPFile
Show-SCOMPropertyBag
I’m off to unseal my repository, so my Notepad++ searches can find more examples for new authoring functionality.