Category: Best Practice
SQL STIG vulnerabilities V-213902, V-213935
DISA DOD SQL STIG vulnerabilities V-213902, V-213935
SCOM SECURITY Documentation
SCOM2019 https://kevinholman.com/2020/07/23/scom-2019-security-account-matrix/
Both V-213902 AND V-213935 state same identification action.
V-213935 has a different identifier:
Tab delimited view –
January addendum updates
First, the biggest change item for large enterprise environments included a change in syntax for get-SCOMAlert
Second, another change with the repo’s was a ‘whitespace audit’ encoded characters, or ‘data concealment’. See AT&T link CyberSecurity Link
Third, after whitespace we focused on script/workflow efficiencies seen in large enterprise environments. While Efforts began in December, the workflow efficiencies sprint resulted in two sets of improvements.
Repo’s updated in January
Links below to GitHub repositories (repo’s)
Improving SCOM Monitor reset logic

My thanks to Aris Somatis for his deep dive reviewing the packs with me, particularly new use cases. The PowerShell below builds on Scott Murr’s initial TechNet published logic from years back. Consequently, the reset logic provides a ‘manual intervention required’ alerting/monitoring system.
Improving SCOM monitor reset logic
Calling the reset method has been a game changer for my customers – including operators, system and application owners!
Background
Scott’s reset logic, from SCOM2012, helped administrators reset unhealthy monitors where alerts may have been closed. Because Scott leveraged the ResetMonitoringState method, the community gained a way to keep true health. Additionally, many administrators and engineers built custom management packs to provide solutions. Second, the addendum packs blog brought in more options – best practices, lessons from the field (and customers), and health model accurate alerting for what was really broken in the environment. Third, addressing ‘gaps’ or ‘blind spots’ from product teams. As a result of NEW monitoring, the packs may include: rules/monitors, datasource/writeAction (DS/WA) workflows, recovery tasks and automation, count logic monitors, overrides, discoveries, and groups. Thirdly, to take monitoring to the next level. To top that off, with very little/NO cost compared to competitors!
PowerShell code
Aris’s Age use case takes this even further. Using monitor age allows further analysis to dial down ‘monitor reset’ to object is X days old. Comparatively, the 24-72 hour setup default is used in the addendums, so Age provides a second option. Third option can rely on SCOM’s built-in cleanup, but that’s typically 14-30 days. Overall, flexibility is a good thing.
# Specify age variable for your environment
$Age = [DateTime](Get-Date).AddDays(-7)
PowerShell code snippet
First, the reset logic can pivot on the age requirement. Then, adjust the Age variable per requirements. Third, figure out which method applies to gather a unique list of classes, whether by partial string(s), or by management pack name(s).
Set age variable (how long ‘OLD’ monitors might be stale and need reset)
# Example sets $Age variable to 7 days ago (-7)
$Age = [DateTime](Get-Date).AddDays(-7)
Unpack two different ways to gather classes for monitors to reset
# When common string name exists in all classes
Example DFS/FileServices packs all have one of the three strings:
# DFS pack naming
$DFSClasses = @(Get-SCOMClass -Name “*FileServices*”; Get-SCOMClass -Name “*FileServer*”; Get-SCOMClass -Name “*DFS*” )
$DFSClass = $DFSClasses | sort -property Name -uniq
# Debug
$DFSClass.Count
# Get AD classes – Microsoft.Windows.Server.AD.2016.Discovery, Microsoft.Windows.Server.AD.Library
$ADLibrary = Get-SCOMManagementPack -name “Microsoft.Windows.Server.AD.Class.Library”
#get-scomclass -ManagementPack $ADLibrary
$ADMonitoring = Get-SCOMManagementPack -name “Microsoft.Windows.Server.AD.2016.Monitoring”
#get-scomclass -ManagementPack $ADMonitoring | fl DisplayName,Name,ID
$ADDiscovery = Get-SCOMManagementPack -name Microsoft.Windows.Server.AD.2016.Discovery
#get-scomclass -ManagementPack $ADDiscovery | fl DisplayName,Name,ID
# ADDS pack naming
$ADDSClasses = @(Get-SCOMClass -ManagementPack $ADLibrary; Get-SCOMClass -ManagementPack $ADDiscovery; )
# NOTE Excluded AD Monitoring pack as NO classes existed
$ADDSClass = $ADDSClasses | sort -property Name -uniq
# Debug count of unique classes
$ADDSClass.Count
Reset monitor PowerShell screenshot
Download from GitHub https://github.com/theKevinJustin/SCOMMonitorReset

Example PowerShell on HealthService resets
NOTE debug logic enabled
0 Found 0 unhealthy monitors for class Microsoft.SystemCenter.HealthServicesGroup 1 Found 1 unhealthy monitors for class Microsoft.SystemCenter.HealthServiceWatcher Resetting Health State on ' + Microsoft.SystemCenter.HealthServiceWatcher:Microsoft.SystemCenter.AgentWatchersGroup;5e0 4f804-8b71-6eb6-0101-dcbb58022498 + ' Guid ---- 0218d239-3d37-f9b1-75d2-6d52c2c7c0c1
Documentation/Sources
PowerPoint soft skills

Do you have expert PowerPoint soft skills? Are you an expert presenter? I’ll bet there’s at least one item here you might not know. Fortunate to have spent some time learning from Asia Platt, Brittany Holloway, and Mauricio Fuentes about expert presentations. Let’s go over some tips and tools to improve what you present, for more interaction, clarity, and more.
Quick Overview
Magnification tools like Magnifier, ZoomIt, and Teams
Laser pointer in PowerPoint
Rehearse and record PPT slide deck
Soft Skills tips and tricks
Magnification tools
Zoom – Can you see this?
Various methods for Zooming (including Teams)

Do you struggle with demo’s to present screens that customers struggle to view? See some magnifier tool options from windows client/server, teams, and PowerPoint below.
Magnifier (on Windows client/servers)
Click on Start > type Magnifier
Change zoom level
Move mouse to focal point

BE careful and don’t move mouse too much!!
ZoomIt
Good utility for demo’s and presentations. Zoom, draw, whiteboard, type pen (in colors), and more
ZoomIt SysInternals free tool download https://learn.microsoft.com/en-us/sysinternals/downloads/zoomit
Shortcuts link

Teams built in Zoom
My own personal preference is Teams. Demo’s can work in a pinch if only Magnifier is involved in a lab demo.
Zoom in/out of Teams shared application/screen https://support.microsoft.com/en-us/office/zoom-in-and-out-in-microsoft-teams-dc3cd3d8-efb5-4995-8b31-434b3943ba52

Laser pointer in PowerPoint
Hit the Control Key to turn your mouse into a pointer, allowing your audience to know ‘what’ is being emphasized.
Click Control, or Control-L for Laser pointer when presenting in PowerPoint.

Rehearse with coach
Record PPT slide deck
Asia (Asha) suggested this method to record delivery for analysis. This helps check tone, pace, filler words, and more.
From PowerPoint, click on Slide Show > Rehearse with coach
PowerPoint Rehearse – record and get analysis from practicing your presentation.Go through presentation, and view analysis

Second page screenshot of more details

Soft Skills tips and tricks
- PowerPoints ‘Rehearse with Coach’ is an awesome way to practice and level set delivery.
- Magnification tools – Magnifier, ZoomIt, Teams (built in Zoom)
- Be creative and be yourself in delivery!

3. Involvement

Involvement example
Interaction soft skill – personalization.
I utilized this to reinforce (from my introduction), as an audience check in, gauging involvement. This helped me gauge where the audience was attention wise. Required audience thought before answering.

Hope this article provided another tool in the Presentation Soft Skills toolbox!
Hope this gave another tool in the Presentation Soft Skills toolbox!
Delete PKI certificates

Man, I wish I had a few of these certificates in my PKI infrastructure (portfolio)! Ever need to identify an expired certificate, and or delete the certificate? Depending on UAC, AppLocker, and other settings, the delete portion may require server logon.
Identify an expired certificate
Few ways to identify an expired certificate on servers.
Via RDP session to server
RDP to server, open MMC > Add Plug In > Certificates > for Computer

Via PowerShell
GCI Cert:\LocalMachine\*
The certificate store file path will vary the above command.
NOTE the SuperUser blog post will help decipher the folder name
Via ‘smart’ PowerShell across multiple machines
Courtesy of Vance Cozier!
“server1”,”server2″| % {invoke-command $_ -scriptblock {$env:ComputerName; GCI Cert:\LocalMachine\* }}
Via Monitoring for expired certificates
Using SCOM Certificate Monitoring or PKI monitoring management packs
Identify Expired certificates
Console navigation steps:
From SCOM console > Monitoring Tab
Expand PKI folder > Expand Certificates and CRLs folder
Click on ‘Certificates – Expired’ state view

Did you know
Run PowerShell commands from Holman’s SCOM Management pack (blog)- github download
Run PowerShell from Monitoring tool
From SCOM console > Monitoring Tab > SCOM Management folder > SCOM Agents
Highlight agent(s)
From Tasks Pane > click on ‘Execute any PowerShell’ task

On the pop-up window, click Override
Adjust timeout to 70 (seconds)
Override command line
Run the following commands (various Certificate store examples provided for removing expired certificates)
Personal Certificates folder
Get-ChildItem Cert:\LocalMachine\My | ? { (( $_.Subject -like “*GlobalSign*” ) -OR ( $_.Issuer -like “*GlobalSign*” )) -and $_.NotAfter -lt (get-date) } | fl Subject,Issuer
Trusted Root folder
Get-ChildItem Cert:\LocalMachine\Root | ? { ( $_.Subject -like “*GlobalSign*” ) -OR ( $_.Issuer -like “*GlobalSign*” ) } | fl Subject,Issuer
Third Party Root
Get-ChildItem Cert:\LocalMachine\AuthRoot | ? { (( $_.Subject -like “*GlobalSign*” ) -OR ( $_.Issuer -like “*GlobalSign*” )) -and $_.NotAfter -lt (get-date) } | fl Subject,Issuer

Click OK button to close Overrides window
Click OK to run task
View task output
PS C:\Users\admin> Get-ChildItem Cert:\LocalMachine\Root | ? { ( $_.Subject -like “*GlobalSign*” ) -OR ( $_.Issuer
like “*GlobalSign*” ) } | fl Subject,Issuer
Subject : CN=GlobalSign Root CA, OU=Root CA, O=GlobalSign nv-sa, C=BE
Issuer : CN=GlobalSign Root CA, OU=Root CA, O=GlobalSign nv-sa, C=BE
Subject : CN=GlobalSign, O=GlobalSign, OU=GlobalSign Root CA – R2
Issuer : CN=GlobalSign, O=GlobalSign, OU=GlobalSign Root CA – R2
Once task completes, go back to the Certificates state view > highlight the certificate > Click the Rediscover Certificates task

Delete PKI certificates
After identifying correct certificate and folder in question that requires deletion:
- Verify backup of certificate
- Test delete via PowerShell window from SCOM
Get-ChildItem Cert:\LocalMachine\AuthRoot | ? { ( $_.Subject -like “*GlobalSign*” ) -OR ( $_.Isser -like “*GlobalSign*” ) } | Remove-Item -DeleteKey
- Verify Task output shows certificate deleted
- Refresh MMC GUI > Certificates plug in, and folder to verify certificate deleted
- Go back to SCOM Console Monitoring Tab
- Expand PKI folder
- Expand Certificates and CRLs folder
- Click on Certificates – Expired state view
- In Tasks pane on right, click on Rediscover certificates task, Click OK to run
- Open Health Explorer and reset monitor to clear alert
Alternatively, leverage PowerShell reset logic on SCOM MS, use blog
Documentation
SCOM Certificate monitoring TechCommunity blog https://techcommunity.microsoft.com/t5/system-center-blog/scom-management-pack-for-certificate-monitoring/ba-p/3619299
Download SCOM Certificate monitoring pack https://www.microsoft.com/en-us/download/details.aspx?id=104858
Long-standing PKI certificate pack and blog https://blog.topqore.com/new-version-pki-certificates-monitoring-pack-for-scom/
Identify certificate stores to windows folders https://superuser.com/questions/217719/what-are-the-windows-system-certificate-stores
STIG finding V-69223 https://www.stigviewer.com/stig/zos_tss/2016-06-30/finding/V-69223
Updated DNS2012R2 Addendum

Updated DNS2012R2 Addendum overrides. Learned a few new things with Overrides workspace views, and why Authoring pane > Management pack Objects > Overrides may not load.
When your management pack has improper overrides, expect the loading icon. This may be caused due to overrides, whether error is with target, class/rule/monitor.

Sometimes, an Object of class error gets your hopes up (pointing at a non-existent object).

Example when Overrides loads properly

If Overrides view will not load, try creating a workspace view for Overrides.
Navigation Steps:
From SCOM Console
Click on My Workspace
Right Click > New > Overrides Summary View

Select checkbox ‘with a specific override management pack’ checkbox, then the ‘specific’ link to choose management pack(s).
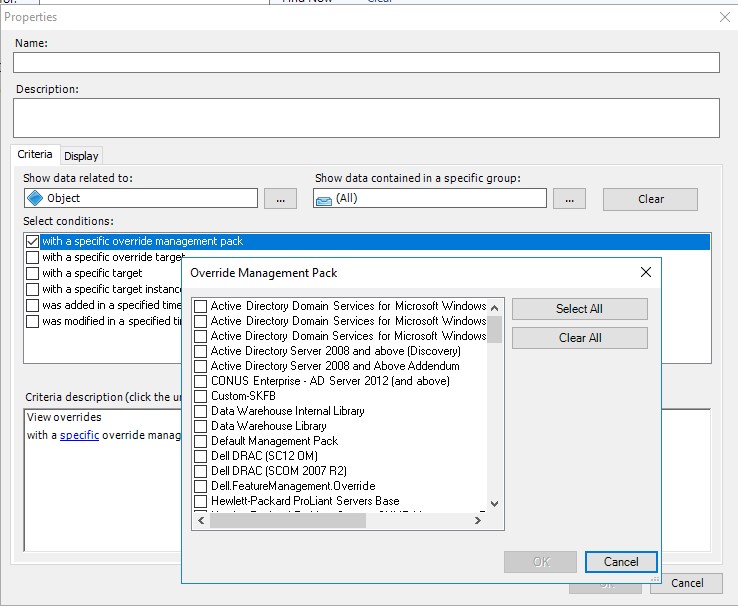
Choose unsealed management pack(s) with overrides
Can select all – OR pick a few to see what loads without errors
Click OK
If you get the loading screen and error, now begins the pack analysis.

Clicking on the ‘Show’ link points to a non-existent object
Microsoft.EnterpriseManagement.Common.ObjectNotFoundException: An object of class ManagementPackClass with ID 76e2559c-aaf4-b1ec-60cf-d40ab4102fbc was not found.
How did I know that?
Run get-SCOMClassInstance command from PowerShell or Operations Manager shell
Example output of ‘get-SCOMClassInstance -ID “76e2559c-aaf4-b1ec-60cf-d40ab4102fbc” ‘
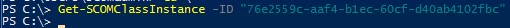
Work on the Overrides of the affected XML packs, and Import.
Once corrected, the Workspace view loads successfully, finite!

Documentation
My Workspace https://learn.microsoft.com/en-us/system-center/scom/manage-web-console-my-workspace?view=sc-om-2022
Monitoring workspace https://learn.microsoft.com/en-us/system-center/scom/manage-using-monitoring-workspace?view=sc-om-2022
NiCE VMware addendum

‘NiCE VMware addendum’ enhances VMware monitoring, tuning alerts to ‘manual intervention’ required alerting. The NiCE folks have been around for some time as a trusted Microsoft partner, creating additional monitoring functionality across Microsoft products. Having completed a number of projects implementing the VMware pack, it’s time to share the configuration and alert report capabilities.
Quick Download HTTPS://GITHUB.COM/THEKEVINJUSTIN/NICEVMWAREADDENDUM/
Changes to Nice vmware pack
Key breakdown of VMware ESX environment monitoring

Adjustments to vendor pack to further the mantra ‘alert when manual intervention required’.
Set monitor alerts to multiple samples over an hour (i.e. compute and performance of ESX environment)
Reports by team (requires regular expression updates for environment servers owned by each team)
Monitor reset logic, and service monitorType (count logic for X failures over Y time, before alert)
Overrides to change vendor pack provided discoveries, rules, monitors
Remove alert noise for unmanaged objects in ESX environment
Customize pack for environment
Customize the ‘NiCE VMware addendum’ pack for specific environment. This means updating group discoveries, and GUIDs for group specific overrides. Further updates are required to update server naming conventions for team virtualization reports.
Classes/groups created for pack
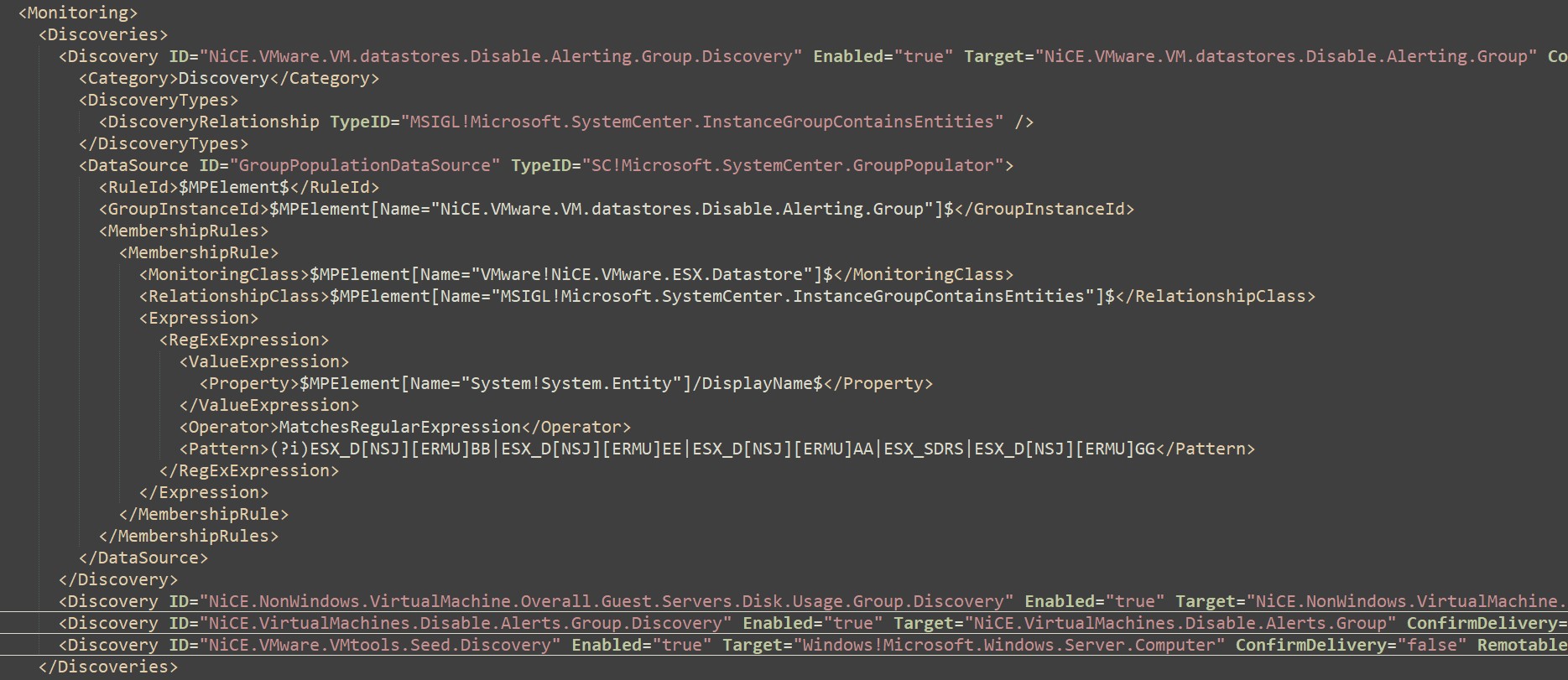
Discoveries
Breakout of Discoveries that need pattern updates to match
Find/Replace ##ESXHostDataStoreNamingConventions## with names to exclude
Example of regular expressions for multiple customers
Update disable guest machine alerts
Disable guest machines in ESX environment to disable alerts.
Find ##ESXGuestServersDiskUsageNamingConventions##
Replace with relevant guest naming conventions
Example template/guest/virtual machine names typically disabled
Service MonitorType
Service MonitorType adds Samples and Intervals to alert after consecutive failures (x failures in y minutes then alert )
Rules, Monitors, Recoveries
List of workflows used to troubleshoot/resolve problems
Documentation
NiCE VMware management pack https://www.nice.de/nice-vmware-mp/
File Services Addendum

‘File Services Addendum’, named Microsoft Windows Server FileServices 2016 Addendum, adds replication health/backlog script, seed and group classes, replication/service monitors, recovery tasks, and overrides to tune monitored environment.
Quick Download HTTPS://GITHUB.COM/THEKEVINJUSTIN/FILESERVICESADDENDUM
Overview of File Services monitoring
Addendum assumes the file services version agnostic version 10. pack is installed.
Looking at XML file in Notepad++, the pack references are what packs the workflows refer to (other management packs). Kevin Holman taught building backwards compatibility with MP authoring. Backwards compatibility allows SCOM2012+ import without errors. To take this one step further, the v10.0.0.0 file services packs referenced represent the version agnostic packs.
NOTE: File Services Addendum references may need updates if the whole file services management packs are NOT installed.
References screenshot
Addendum logic
Capabilities
Daily report and close automation, on-demand tasks for reports
DFS backlog script errors
SmSvc, DFSN, DFSR service recovery and rule alerts (from Holman fragments library)
DFS replication backlog watcher, script, alerts
Notepad++ screenshot
Next, we look at the group/class discoveries

Update Class/Group discoveries for DFS servers or script install paths for replication script.
Find and replace FilePath and ##DFSServerNamingConvention## variable.
Save file and Import
Documentation
Kevin Holman MP authoring with fragments https://kevinholman.com/2019/01/17/mp-authoring-with-fragments-introducing-combo-fragments/
Kevin Holman MP fragment library https://github.com/thekevinholman/FragmentLibrary
Addendum GitHub Repository HTTPS://GITHUB.COM/THEKEVINJUSTIN/FILESERVICESADDENDUM