🚀 System Center 2022 UR3 Released: What You Need to Know
Microsoft has officially released System Center 2022 Update Rollup 3 (UR3), and it’s time to update your environments—especially if you’re focused on monitoring with SCOM (System Center Operations Manager).
📅 Support Lifecycle Highlights
- SCOM 2019: Extended support until 2029
- SCOM 2022: Extended support begins in 2027
- SCOM 2025: Extended support starts in 2030, ending in 2035
🔧 SCOM 2022 UR3 Key Fixes
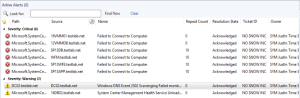
This update brings several important improvements:
- ✅ Fixed Favorite Reports failure in Web Console due to HttpParseException
- ✅ Resolved Teams notifications issues from UR2
- ✅ Addressed random crashes in global search caused by NullReferenceException
- ✅ You can now add Dashboards to Workspace (previously blocked in UR1)
- ✅ Dashboard Performance widget now functions correctly
- ✅ Fixed WMIProbe workflow failures
- ✅ Unix/Linux computers view now opens properly in Web Console
📥 Download & Resources
- Download UR3: https://www.catalog.update.microsoft.com/Search.aspx?q=5055455
- Support Article: https://support.microsoft.com/en-us/topic/update-rollup-3-for-system-center-2022-operations-manager-778f5f8b-ed9f-4a34-b742-48e48fce1b81
- Tech Community Blog: https://techcommunity.microsoft.com/blog/systemcenterblog/system-center-2022-update-rollup-3/4447726
Technical Deep Dive
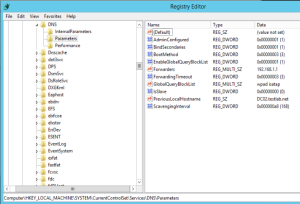
UR3 resolves a critical issue where global search in the SCOM console would crash due to a NullReferenceException. This fix improves stability for large-scale deployments. Additionally, the WMIProbe workflow fix ensures smoother data collection from Windows endpoints.
💬 Community Engagement
What’s your favorite fix in UR3?
Share your thoughts in the comments below or join the discussion on Viva Engage ‘Have you applied UR3 yet?’
Pro Tip: Use PowerShell scripts to automate dashboard deployment post-update.
📣 Call to Action
Subscribe to the blog for monthly insights on monitoring, automation, and Microsoft ecosystem updates. Stay ahead with expert tips and community-driven solutions.
🧠 Final Thoughts
System Center 2022 is now on a yearly update cadence, unless urgent security patches are needed. If you’re running SCOM 2022, this UR3 release is a must-have to stabilize and enhance your monitoring capabilities.