With domain joined machine, use a separate notification services svc account for notifications. SCOM is typically leverages MSAA, or even local system, depending on the accounts used when building out SCOM. Kevin Holman did an excellent job blogging this here
Verify SCOM notification account
Verify and ‘Setup SCOM Notifications account’ to separate notifications outside typical SCOM service SVC account functionality. Also, separating allows CredentialManager to secure, encrypt, and store credentials used by the notification account. Time to verify!
RDP to SCOM MS using notification account.
Open SCOM Console
Click on Administration tab
Expand Run As Configuration
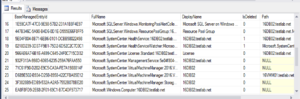
Click on Accounts
Search for notification
Double click on Notifications account
Click on Credentials tab
Verify account being used, in light of CredentialManager piece storing SNOW ID and account.
NOTE Account should be part of SCOM Admins AD group

SCOM Notifications Event Log troubleshooting
Knowing the notifications account will aid with SNOW integration scripts, as well as help log whoami, ‘run as’ logging to the ‘Operations Manager’ event log. The specific test and event or incident scripts leverage EventID’s 710-712. 710 for LogAlert.ps1, 711 for New-SNowEvent.ps1, and 712 for New-SNowIncident.ps1.
Single Starting event indicates failed pre-requisite (pre-req NOT met)

Additional SCOM Notifications documentation
Learn articles
Additional blog posts explaining ServiceNow connectivity
PreReqs https://kevinjustin.com/blog/2024/05/30/snow-rest-integration-prerequisites/
Network and Credential https://kevinjustin.com/blog/2024/05/30/snow-rest-connectivity/
Event Integration https://kevinjustin.com/blog/2024/03/27/servicenow-event-integration/
Incident Integration https://kevinjustin.com/blog/2024/03/27/servicenow-incident-integration/
ServiceNow Connector https://kevinjustin.com/blog/2024/04/30/servicenow-connector-for-scom/