Time to ‘Test SNOW script’ for event or incident injection. As long as the prerequisites are verified, to include network connectivity, URL, ID, Password, etc., we’re ready to go!
Once the CredentialManager piece has been completed, by the same token you can begin testing the script. Testing can begin, whether to the SCOM Admin SA account, or to the SCOM Notifications account, or even hard coding the values into your PowerShell session.
Begin script testing
The testing leverages that you’ve downloaded various integration scripts first, then being saved on SCOM MS (management servers). The following blog posts, GitHub repo’s will set up multiple methods to test from PowerShell (command line) as SA or SVC accounts.
Create new SCOM Command Channels
LogAlert.ps1 from Kevin Holman’s blog https://kevinholman.com/2021/08/25/what-account-will-command-channel-notifications-run-as-in-scom/
New-SNowEvent GitHub repository https://github.com/theKevinJustin/New-SNowEvent
New-SNowIncident.ps1 GitHub repository https://github.com/theKevinJustin/New-SNOWIncidents
Once files are saved, copy to SCOM MS (noting path for later tests).
Preferred choice is non-system disk (i.e. D:)
Lab example is C:\MonAdmin\Scripts
RDP to server with SVC or SCOM Admin SA account
Open PowerShell as administrator
- Change directory to script directory on SCOM MS
cd \ ; cd MonAdmin/scripts

- Inventory saved files via dir (gci):
gci New-SNOW[ie]*.ps1
gci LogAlert.ps1
![dir gci New-SNow[ie]*.ps1](https://kevinjustin.com/blog/wp-content/uploads/2024/05/New-SNOWie.png)
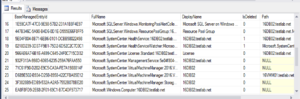
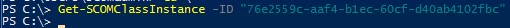
- Grab Critical alert from $Alerts array
$Alerts = get-scomalert -ResolutionState 0 -severity 2
# Test warning events with Severity 1
# $Alerts = get-scomalert -ResolutionState 0 -severity 1
$AlertID = $Alerts[0].ID
$AlertName = $Alerts[0].Name
$AssignmentGroup = “JustinTime Infra”

- Test script supplying variables
.\New-SNowEvent.ps1 -AlertID $AlertID -AlertName $AlertName -AssignmentGroup $AssignmentGroup -Team SYM
.\New-SNowIncident.ps1 -AlertID $AlertID -AlertName $AlertName -AssignmentGroup $AssignmentGroup -Team SYM

Verify SCOM alert updated for ServiceNow REST injection
Check SCOM console/web console for SCOM alert updates to ResolutionState, TicketID, Owner fields, where TEAM = SYM, and Assignment Group = JustinTime Infra specified

Be aware of issues
Indicator of Certificate/trust issue

Indicator when SNOW alert rule not configured or matching – excessive retry’s. Also note output shows summary of tests, ServiceNow SNOW detail, and SCOM alert updates.

Logging to Operations Manager Event Log for addtional troubleshooting or debug. Unless otherwise updated, the script logs to the ‘Operations Manager’ event log, EventID = 710-712
Single Starting event indicates failed pre-requisite (pre-req NOT met)

Additional information